In connection with my handheld > server app using Web API RESTful methods problem discussed here (Does an ASP.NET Web API app need to be installed into the "real" IIS before a handheld device can access its RESTful methods?), I tried to verify I wasn't having a firewall problem by using the shell command delineated here: http://www.hanselman.com/blog/WorkingWithSSLAtDevelopmentTimeIsEasierWithIISExpress.aspx, explicitly:
netsh firewall add portopening TCP 80 IISExpressWeb enable ALL
I also did it using port 777, as that is the one I've got set up in applicationhost.config:
<bindings>
<binding protocol="http" bindingInformation="*:28642:localhost" />
<binding protocol="http" bindingInformation="*:777:192.168.125.50" />
<binding protocol="https" bindingInformation="*:44300:localhost" />
</bindings>
Doing so, I got this fingerwag from the command shell:
IMPORTANT: Command executed successfully. However, "netsh firewall" is deprecated; use "netsh advfirewall firewall" instead.
So, I then entered the following (the traditional/default port 80, as shown in Hanselmann's post, and then the one I added to applicationconfig.host when the trad was failing (777)), one after the other:
netsh advfirewall firewall add portopening TCP 80 IISExpressWeb enable ALL
netsh advfirewall firewall add portopening TCP 777 IISExpressWeb enable ALL
However, after entering the command shell's command (or suggestion), I then got the following feedback from the cmd shell (both times):
The following command was not found: advfirewall firewall add portopening TCP 80 IISExpressWeb enable ALL.
So it tells me to use the newfangled command, then says there's no such thing! What is the story on this? Is there a way to actually use the new command? Is my syntax wrong with it, or...???
Typing netsh /? at a command prompt explains the options available, and that to view information on the option you want to type netsh <option> /?. Doing so with
I:\>netsh advfirewall /?
The following commands are available:
Commands in this context:
? - Displays a list of commands.
consec - Changes to the `netsh advfirewall consec' context.
dump - Displays a configuration script.
export - Exports the current policy to a file.
firewall - Changes to the `netsh advfirewall firewall' context.
help - Displays a list of commands.
import - Imports a policy file into the current policy store.
mainmode - Changes to the `netsh advfirewall mainmode' context.
monitor - Changes to the `netsh advfirewall monitor' context.
reset - Resets the policy to the default out-of-box policy.
set - Sets the per-profile or global settings.
show - Displays profile or global properties.
The following sub-contexts are available:
consec firewall mainmode monitor
To view help for a command, type the command, followed by a space, and then
type ?.
You can apply <command> /? deeper, such as netsh advfirewall firewall /?, which leads to 'netsh advfirewall firewall add /?`, which leads to
I:\>netsh advfirewall firewall add rule /?
Usage: add rule name=<string>
dir=in|out
action=allow|block|bypass
[program=<program path>]
[service=<service short name>|any]
[description=<string>]
[enable=yes|no (default=yes)]
[profile=public|private|domain|any[,...]]
[localip=any|<IPv4 address>|<IPv6 address>|<subnet>|<range>|<list>]
[remoteip=any|localsubnet|dns|dhcp|wins|defaultgateway|
<IPv4 address>|<IPv6 address>|<subnet>|<range>|<list>]
[localport=0-65535|<port range>[,...]|RPC|RPC-EPMap|IPHTTPS|any (default=a
ny)]
[remoteport=0-65535|<port range>[,...]|any (default=any)]
[protocol=0-255|icmpv4|icmpv6|icmpv4:type,code|icmpv6:type,code|
tcp|udp|any (default=any)]
[interfacetype=wireless|lan|ras|any]
[rmtcomputergrp=<SDDL string>]
[rmtusrgrp=<SDDL string>]
[edge=yes|deferapp|deferuser|no (default=no)]
[security=authenticate|authenc|authdynenc|authnoencap|notrequired
(default=notrequired)]
Remarks:
- Add a new inbound or outbound rule to the firewall policy.
- Rule name should be unique and cannot be "all".
- If a remote computer or user group is specified, security must be
authenticate, authenc, authdynenc, or authnoencap.
- Setting security to authdynenc allows systems to dynamically
negotiate the use of encryption for traffic that matches
a given Windows Firewall rule. Encryption is negotiated based on
existing connection security rule properties. This option
enables the ability of a machine to accept the first TCP
or UDP packet of an inbound IPsec connection as long as
it is secured, but not encrypted, using IPsec.
Once the first packet is processed, the server will
re-negotiate the connection and upgrade it so that
all subsequent communications are fully encrypted.
- If action=bypass, the remote computer group must be specified when dir=i
n.
- If service=any, the rule applies only to services.
- ICMP type or code can be "any".
- Edge can only be specified for inbound rules.
- AuthEnc and authnoencap cannot be used together.
- Authdynenc is valid only when dir=in.
- When authnoencap is set, the security=authenticate option becomes an
optional parameter.
Examples:
Add an inbound rule with no encapsulation security for messenger.exe:
netsh advfirewall firewall add rule name="allow messenger"
dir=in program="c:\programfiles\messenger\msmsgs.exe"
security=authnoencap action=allow
Add an outbound rule for port 80:
netsh advfirewall firewall add rule name="allow80"
protocol=TCP dir=out localport=80 action=block
Add an inbound rule requiring security and encryption
for TCP port 80 traffic:
netsh advfirewall firewall add rule
name="Require Encryption for Inbound TCP/80"
protocol=TCP dir=in localport=80 security=authdynenc
action=allow
Add an inbound rule for messenger.exe and require security
netsh advfirewall firewall add rule name="allow messenger"
dir=in program="c:\program files\messenger\msmsgs.exe"
security=authenticate action=allow
Add an authenticated firewall bypass rule for group
acmedomain\scanners identified by a SDDL string:
netsh advfirewall firewall add rule name="allow scanners"
dir=in rmtcomputergrp=<SDDL string> action=bypass
security=authenticate
Add an outbound allow rule for local ports 5000-5010 for udp-
Add rule name="Allow port range" dir=out protocol=udp localport=5000-5010
action=allow
I'm just adding this for future "generations" - I wish I could divide the answer check with Ken White and admdrew; the first did so much work, I think I will give it to him, although both answers were good. I actually found what I needed though in a comment appended to Hanselmann's post referenced at the top of my question (by Blake, etwa 60% of the way down the page).
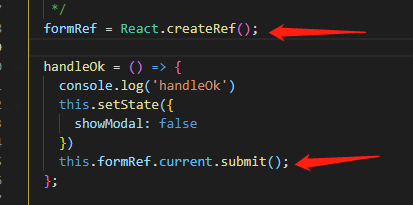
I had to enter "cmd" in the Start > Run box, mash Ctrl+Shift+Enter to run the shell as administrator, and then enter these commands:
netsh advfirewall firewall add rule name="IISExpressWeb" dir=in protocol=tcp localport=80 profile=private remoteip=localsubnet action=allow
netsh advfirewall firewall add rule name="IISExpressWeb" dir=in protocol=tcp localport=777 profile=private remoteip=localsubnet action=allow
They ran with no squawking from the Microsoft elves that live inside the console (they meekly echoed back a simple, "Ok." after I pasted them and ran them).
Looks like it's just a syntax thing; portopening isn't a valid option for advfirewall. Check out:
- http://technet.microsoft.com/en-us/library/dd734783%28v=ws.10%29.aspx
- http://support.microsoft.com/kb/947709
Running netsh advfirewall firewall add rule /? from the command line will also give you a bunch of syntax information.