Im re-writing a file hosting site, and I want to have the ability to host every single file type (instead of just having a whilelist of allowed extensions).
Im running nginx and linux. Site is built in php. I'd disable th upload of .php files.... but other than that.... is there anything else I should watch out for?
A cleaner maneer to solve the problem would be to setup a subhost (something like files.somewhere.com) or a directory, and disable execution via a .htacess (Users will be able to upload php script, but the server will send it instead of executing it).
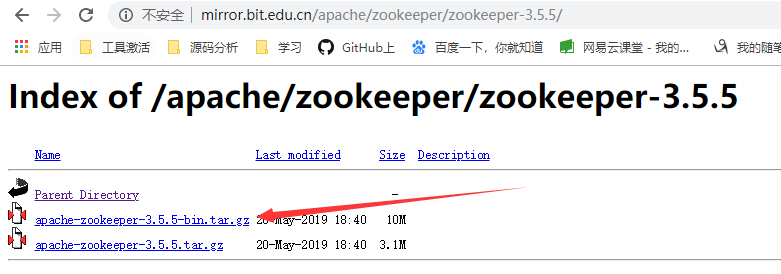
Here's a list of the extensions we tend to block on our php file upload system.
1st you would be best to save the files in a none accessible folder that way no one can run any files uploaded and second do a force download of every file, that way it can't be opened either.
Extension list :
bat
exe
cmd
sh
php
pl
cgi
386
dll
com
torrent
js
app
jar
pif
vb
vbscript
wsf
asp
cer
csr
jsp
drv
sys
ade
adp
bas
chm
cpl
crt
csh
fxp
hlp
hta
inf
ins
isp
jse
htaccess
htpasswd
ksh
lnk
mdb
mde
mdt
mdw
msc
msi
msp
mst
ops
pcd
prg
reg
scr
sct
shb
shs
url
vbe
vbs
wsc
wsf
wsh
Also here is a Javascript regular expression of the above:
/(\.|\/)(bat|exe|cmd|sh|php([0-9])?|pl|cgi|386|dll|com|torrent|js|app|jar|pif|vb|vbscript|wsf|asp|cer|csr|jsp|drv|sys|ade|adp|bas|chm|cpl|crt|csh|fxp|hlp|hta|inf|ins|isp|jse|htaccess|htpasswd|ksh|lnk|mdb|mde|mdt|mdw|msc|msi|msp|mst|ops|pcd|prg|reg|scr|sct|shb|shs|url|vbe|vbs|wsc|wsf|wsh)$/i
The best way here is a combination of:
- Disable execution in your upload dir.
- Rename all files that you suspect: PHP, SH, BIN, etc or store all files compressed in ZIP/TAR files.
- Use an antivirus (Dr. Web, ClamAV, etc) on the server and scan files regularly.