I have made an ASP.NET MVC 3 Intranet site with Windows Authentication enabled:
- in the Visual Studio project file properties
- in the web.config, i.e.
<authentication mode="Windows"/>
- on the site properties in the IIS 7.5. server
Anonymous access is disabled for all these three above, the web.config says <deny users="?"/>. Impersonation is disabled in the web.config by identity <impersonate="false"/> and on the site properties in the IIS 7.5 server. And finally, the NETWORK SERVICE is set to run the app pool and also has Read on the site folder (not sure if it's needed though, you tell me, but it sure ain't enough to solve my problem below).
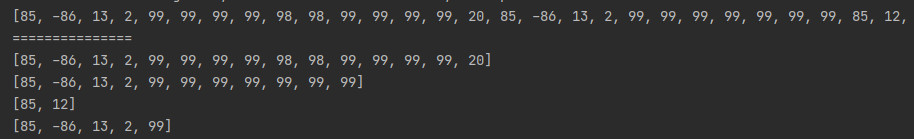
Now, when logging in through the standard Windows Authentication dialog box, domain users are presented with a 401.3 error after three valid login attempts. This seems to be before even reaching my MVC site's code, i.e. it seems completely IIS related. The event log gives the following kind of entry (it's an Information entry, not an Error, and I've obfuscated it a bit to protect my client) for all the users that has tried to log in:
Event code: 4008
Event message: File authorization failed for the request.
Event time: 2012-02-20 18:45:41
Event time (UTC): 2012-02-20 17:45:41
Event ID: 6dd3b4bf99784ba1a0fe06694dd89691
Event sequence: 3
Event occurrence: 1
Event detail code: 0
Application information:
Application domain: /LM/W3SVC/2/ROOT-1-129742335229554599
Trust level: Full
Application Virtual Path: /
Application Path: D:\Public\BlahblahManager\
Machine name: HUB01-XYZ123
Process information:
Process ID: 2920
Process name: w3wp.exe
Account name: NT AUTHORITY\NETWORK SERVICE
Request information:
Request URL: http://blahblahmanager.user.ad.blah.com/
Request path: /
User host address: 134.XXX.XXX.XXX
User: USER-AD\teh-user
Is authenticated: True
Authentication Type: Negotiate
Thread account name: NT AUTHORITY\NETWORK SERVICE
Custom event details:
It is only when I specifically grant USER-AD\teh-user or USER-AD\Domain users the Read permission on the site's root folder (D:\Public\BlahblahManager) that the user can log in and actually see the site.
Why is this? There must be some kind of configuration that I'm missing. Shouldn't it be enough that the NETWORK SERVICE has Read on the site's root folder? I've Googled this for a while, and impersonation is mentioned here and there, but the jury is still out it seems. Some sites claims that you should go with impersonation and they provide examples on how to do it, but when I try out the examples it still doesn't work. Other sites says that impersonation is NOT the way to go and that you NEED to grant the folder permissions in these cases. But that seems such an odd thing to do. Users have no business on the actual server, they should be working through the website only.
Any suggestions? What is usually the minimum amount of configuration needed to get this to work? Any tips on how to troubleshoot this kind of problem and get to the root cause?
I refer you to see this post that declares all of MVC authentication methods. but make sure you have enabled minimum required authentication on your mvc application. Notice that Anonymous Authentication works with your group policies. you can config that by following : Internet Options -> Security Tab -> Local Intranet -> Custom Level, on your browser.
1- Another thing that may causes the problem is IIS may configured not to authorized related users. Some of them are :
- iisservice
- IUSR
- IIS_IUSRS
- Network Service
2- Also Check allowed verbs in IIS.
3- On the root folder of your application Give read access to IIS AppPool\YourAppPool.
4- Another cause could be hierarchical access rules in your application depends on what application services you are using, like web site panel access rules.
5- Setting the clientaccesspolicy.xml file.
6- Check InitializeService() Method, do you set entity access rules properly? For example:
config.SetEntitySetAccessRule("*", EntitySetRights.All);
7- Check FileAuthentication module at the web site level.
Double check Anonymous authentication is enabled on IIS.
Also, have a look at this post.
We were also fighting with this issue, and started setting up security groups so we could give our users file level permissions. Then one of our server admins stumbled across a couple of new properties that allow the app to authenticate to the file system under set credentials, and resolved the need for the users to have access. Here is what he came up with…
There are two IIS settings that control this:
Physical Path Credentials Physical Path Credentials Logon type
By default, Physical Path Credentials is set to Application User
(Pass-through authentication). This means that IIS doesn’t do any
impersonation when handling Windows Authentication requests. This can,
however, be set to a specific user (though not, unfortunately, the
application pool identity, which would be ideal). Physical Path
Credentials Logon Type is set by default to Clear-Text. For my testing
I set this to Interactive (though this may not be the correct value).
Possible values are Clear-Text, Batch, Interactive, and Network.
To set this up I did the following:
- Created a local account (IIS-AccessUser)
- Granted IIS-AccessUser read and execute access to the /home directory of the site.
- Added IIS-AccessUser to IIS_IUSRS group (necessary for accessing .NET temporary files)
- Set IIS-AccessUser as the Physical Path Credentials
- Set Physical Path Credentials Logon Type to Interactive
Doing the above allowed me to log in to the application directly,
without having to allow Authenticated Users, or me having to be a
member of any of the groups in the /home folder. It also still
preserved .NET Authorization roles, so I still could not access parts
of the site that I was not allowed to.
I also faced this same issue on iis7 with windows authentication, but with with MVC4.
Finally found this post. Hope this might help someone in the future.
You are not required to grant file access permissions when using Windows Authentication in IIS 7.0 and IIS 7.5.
There's a better way that we were only able to discover this because our server admin smelled the security and management issues that arise from taking the route of granting file level access to users and groups.
For anyone dealing with this issue or if you are setting up a new IIS7/IIS7.5 server and/or moving from IIS 6, here is an article that gives you all of the Windows Authentication options and configurations that need to be modified to avoid granting file level access to individuals or groups.
Please read the two comments in at the end of the POST for some valid critiques of the methods used in this article.
http://weblogs.asp.net/owscott/iis-using-windows-authentication-with-minimal-permissions-granted-to-disk
In addition to the information in the article, please be aware that IIS 7.5 is not using the web configuration tags for system.web (at least not in my MVC 4 application).
It is looking in the system.webserver tags for authorization configuration (where you will need to list the windows domain\groups a user needs to be in to access your application).
-- DSB