I'm trying to use public/private keys instead of a shared secret for client secrets with IdentityServer4. This approach is documented here.
If it was a shared secret, the request would contain the secret in plain text. e.g.
curl -X POST \
http://<identityserver>/connect/token \
-F client_id=abc \
-F client_secret=secret \
-F grant_type=client_credentials \
-F scope=api1 api2
My question is: What should be passed in as the secret with the public/private key authentication method?
To give some background, a Client using public/key authentication will register with IdentityServer with the following steps
Client generates a .crt file e.g.
// create key
$ openssl genrsa -des3 -passout pass:x -out client.pass.key 2048
$ openssl rsa -passin pass:x -in client.pass.key -out client.key
// create certificate request (csr)
$ openssl req -new -key client.key -out client.csr
// create certificate (crt)
$ openssl x509 -req -sha256 -days 365 -in client.csr -signkey client.key -out client.crt
// export pfx file from key and crt
$ openssl pkcs12 -export -out client.pfx -inkey client.key -in client.crt
Client will share the client.crt file with the IdentityServer
IdentityServer will register the Client by
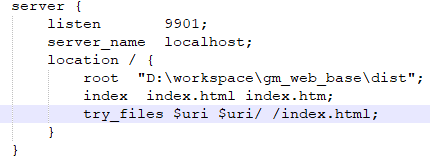
var client = new Client
{
ClientId = "abc",
ClientSecrets =
{
new Secret
{
Type = IdentityServerConstants.SecretTypes.X509CertificateBase64,
Value = "MIIDF...." <================= contents of the crt file
}
},
AllowedGrantTypes = GrantTypes.ClientCredentials,
AllowedScopes = { "api1", "api2" }
};
Figured this out thanks to the unit tests in IdentityServer4!
When using public/private authentication, client_secret is not used. Rather a client_assertion is used, which is a JWT token.
Here is sample code for the token request. client.pfx is the certificate bundle generated from the steps above in the question.
var now = DateTime.UtcNow;
var clientId = "abc";
var tokenEndpoint = "http://localhost:5000/connect/token";
var cert = new X509Certificate2("client.pfx", "1234");
// create client_assertion JWT token
var token = new JwtSecurityToken(
clientId,
tokenEndpoint,
new List<Claim>
{
new Claim("jti", Guid.NewGuid().ToString()),
new Claim(JwtClaimTypes.Subject, clientId),
new Claim(JwtClaimTypes.IssuedAt, now.ToEpochTime().ToString(), ClaimValueTypes.Integer64)
},
now,
now.AddMinutes(1),
new SigningCredentials(
new X509SecurityKey(cert),
SecurityAlgorithms.RsaSha256
)
);
var tokenHandler = new JwtSecurityTokenHandler();
var tokenString = tokenHandler.WriteToken(token);
// token request - note there's no client_secret but a client_assertion which contains the token above
var requestBody = new FormUrlEncodedContent(new Dictionary<string, string>
{
{"client_id", clientId},
{"client_assertion_type", "urn:ietf:params:oauth:client-assertion-type:jwt-bearer"},
{"client_assertion", tokenString},
{"grant_type", "client_credentials"},
{"scope", "api1 api2"}
});
var client = new HttpClient();
var response = await client.PostAsync(tokenEndpoint, requestBody);
var tokenRespone = new TokenResponse(await response.Content.ReadAsStringAsync());
I think it has to be a signed JWT. Check out the PrivateKeyJwtSecretValidator class in the IDS4 codebase:
https://github.com/IdentityServer/IdentityServer4/blob/2.1.3/src/IdentityServer4/Validation/PrivateKeyJwtSecretValidator.cs