I'm running an ASP.NET 4.0 app which uses the user name (i.e. HttpContext.Current.Request.LogonUserIdentity.Name.ToString()) to manage access to various components.
The user name being returned is in the form "abc\jsmith" where "abc" is the domain name and "jsmith" is the login name of the user.
Part of the security module for this app accesses the Active Directory groups that the user belongs to (e.g., "Accounting", "AccountsPayable", "AdminDepartment"). I'm able to get the user's name from Active Directory using the DirectoryEntry.Properties (i.e., System.DirectoryServices.PropertyCollection") "sAMAccountName".Value.
So far, everything is fine, but I want to be able to expand the app across multiple domains, which mean I need to be able to find the domain name in Active Directory as well as the user's Login Name. I can get a "Domain" value from PrincipalContext, but it's returning "abcdc", instead of "abc". Can I assume that this property will always return "dc" (as in "Domain Controller") at the end of each domain (in which case I can use a Substring of the property), or is there somewhere else I can get the user's current domain name?
One thing I am unclear on is your question about retrieving the domain name given a directoryentry in a domain controller. I am assuming that you have a server that can see multiple trusted domains, and that a user can log into your application from any one of them such that you don't know against what domain you need to test role membership.
For controlling access to features via ADGroup membership, could you use the
HttpContext.Current.User.IsInRole("appdomain\groupname")
where User.Identity.Name=="userdomain\user". I'm not familiar with domain trust issues, but this assumes that you can add users from the trusted domain into the domain group that you control so you don't need to worry about the group domain location.
If you can't, or if you have the same group name in each different domain, then you could do something like this?
HttpContext.Current.User.IsInRole(userDomainname + "\groupname")
Some points:
- unless you already have a large established AD codebase, I would recommend using objects from the System.DirectoryServices.AccountManagement namespace.
- I highly recommend the ADExplorer utility from Sysinternals to get a more LDAP view of your domain(s) which helps with LDAP connection strings and directory programming in general.
- If you are comfortable with interop, and need to perform any LDAP connection string parsing, check out this site.
- The System.DirectoryServices.AccountManagement.PrincipalContext.Container and System.DirectoryServices.DirectoryEntry.Path properties return the LDAP connection string w/ the domain at the end of the string (i.e., DC=mycompany,DC=com)
- Don't forget about trusty old Environment.UserDomainName & Environment.UserName (which grabs the WindowsPrincipal from the currently executing thread; see Table 1: Thread Exposed CurrentPrincipal Object @ http://msdn.microsoft.com/en-us/library/Aa480475.aspx for a great table on what the current user is within the asp.net runtime. )
** UPDATE 6/8/2011 2:15 PM**
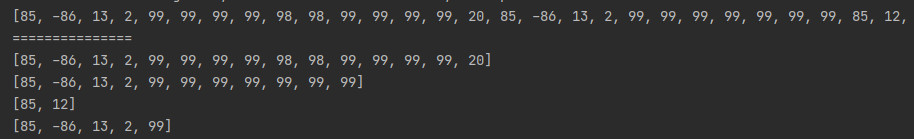
If I understand AD correctly, the user's domain is an integral part of the user object returned by AD. Expanding on your example of "Bob Newaccountant"...
So given the following 2 Domains with a trust between them:
1. "abcdc.com"
CN=Users
CN="Bob NewAccountant"
2. "abc.com"
CN=Users
CN="Local User1"
OU=Applications
OU=MyApplication
CN=ReportReaders (Members: abcdc\BNewAccountant, abc\luser1)
You should get the users' info given the following query:
//name parameter = domain
//container parameter = distinguished name
using(var ctx = new PrincipalContext(
ContextType.Domain,
name: "abc.com",
container: "OU=MyApplication,OU=Applications,DC=abc,DC=com",
"abc\serviceaccountname",
"Password1"))
{
var officeGroup = GroupPrincipal.FindByIdentity(ctx,
IdentityType.SamAccountName,
"ReportReaders");
foreach(Principal prin in officeGroup.GetMembers(recursive: true))
{
Console.WriteLine("DistinguishedName: " + prin.DistinguishedName
+ " UPN: " + prin.UserPrincipalName);
}
//Should result in
// DistinguishedName: CN=luser1,CN=Users,DC=abc,DC=com UPN: luser1@abc.com
// DistinguishedName: CN=BNewAccountant,CN=Users,DC=abcdc,DC=com UPN: BNewAccountant@abcdc.com
}
So you should be able to get the user's domain via distinguishedName or userPrincipalName properties of active directory. (Note: I don't have a dual domain setup handy to me so I am not able to test the above code at this time.) Is that getting closer?
Here is the WMI way to find it. I give you the PowerShell writting, but you can transform it for VBScript or C# easily
PS C:\> (Get-WmiObject Win32_NTDomain).DomainName
Be careful, the Domain part of the 'pre windows 2000 domain' can be completly different from the user Principal Name (user@domain) use to logon onto Active-Directory. the DOMAIN is the Primary Domain Controleur name or the Netbios domain name. DOMAIN is created during domain creation, by default it's part of the DNS name, but it can be completly changed during domain creation.
You can find it with nETBIOSName attribute :
ldifde -f netbios.ldf -d "CN=Partitions,CN=Configuration,DC=your-DNS-Name" -r "(netbiosname=*)"
Edited
Here is the CSharp code
ManagementObjectSearcher domainInfos1 = new ManagementObjectSearcher("select * from WIN32_NTDomain");
foreach (ManagementObject domainInfo in domainInfos1.Get())
{
Console.WriteLine("Name : {0}", domainInfo.GetPropertyValue("Name"));
Console.WriteLine("Computer/domain : {0}", domainInfo.GetPropertyValue("Caption"));
Console.WriteLine("Domain name : {0}", domainInfo.GetPropertyValue("DomainName"));
Console.WriteLine("Status : {0}", domainInfo.GetPropertyValue("Status"));
}
DC stands for domain component. A seemingly decent rundown for programming with Active Directory is here. There's a bit much over there to do a decent copy and paste here, but I did find the following which may help you:
domainname=inputbox("Enter DNS Domain Name" & vbcrlf & "(Leave blank for current domain):")
username=inputbox("Enter username:")
IF domainname = "" THEN
SET objRoot = GETOBJECT("LDAP://RootDSE")
domainname = objRoot.GET("defaultNamingContext")
END IF
IF username <> "" THEN
wscript.echo finduser(username,domainname)
END IF
FUNCTION FindUser(BYVAL UserName, BYVAL Domain)
ON ERROR RESUME NEXT
SET cn = CREATEOBJECT("ADODB.Connection")
SET cmd = CREATEOBJECT("ADODB.Command")
SET rs = CREATEOBJECT("ADODB.Recordset")
cn.open "Provider=ADsDSOObject;"
cmd.activeconnection=cn
cmd.commandtext="SELECT ADsPath FROM 'LDAP://" & Domain & _
"' WHERE sAMAccountName = '" & UserName & "'"
SET rs = cmd.EXECUTE
IF err<>0 THEN
FindUser="Error connecting to Active Directory Database:" & err.description
ELSE
IF NOT rs.BOF AND NOT rs.EOF THEN
rs.MoveFirst
FindUser = rs(0)
ELSE
FindUser = "Not Found"
END IF
END IF
cn.close
END FUNCTION
You could get the users "userprincipalname". It looks like an email address but is actually the samaccountname + @ + domain.name. one thing to note is that the Active Directory domain looks like an internet Domain name, but the netbios domain name (the 'abc' from your example) does not.
If you grab the UPN, I believe it will always contain the dotted domain name.