I am working on Holepunching using UDP and UDT. For the final testing I need to test the application on different NAT types (Symmetric,full cone,restricted cone, port restricted NATs).
Is there any method I can simulate these? What I expect here is some kind of virtual-Box setup. Can I use PC as a router so that I can configure according to my needs?
In general how do we test applications for different network conditions?
I think you already answered your own question, use VirtualBox (or VMware, Xen, etc..).
I've done this very thing successfully by setting up mini-lans of VM's. If you're looking for software to act as your router inside a VM, I'd start off at http://www.pfsense.org/ and see if that meets your needs. It's a FreeBSD distribution tailored for being an easy to install router/firewall with a nice web management UI and all of that.
If pfsense doesn't fit your needs, there are plenty of other linux/bsd distributions out there that are tailored for this kind of stuff and that you can install in a VM: http://en.wikipedia.org/wiki/List_of_router_or_firewall_distributions for a good list :) (I've heard good things about OpenWRT and ClearOS as well.)
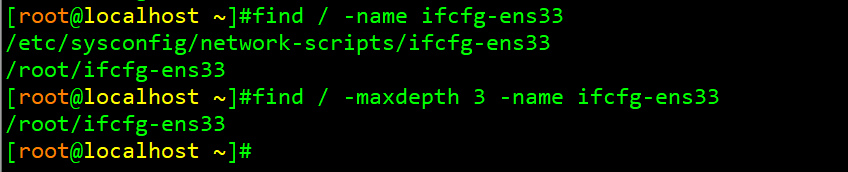
Just in case someone else is looking to do this, this website explains how to set up the different NAT environments using IPTables.
Update
It has been a few years since I did this, given that the link was placed behind a login, and the rewind was also placed behind a login, I went through my notes from back than and found the following. Please note these are untested.
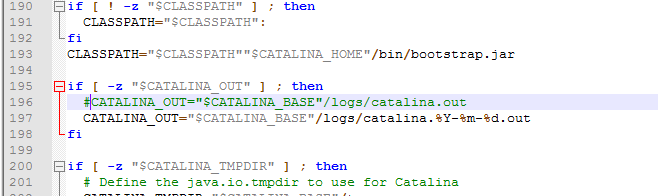
Full Cone NAT;
iptables -t nat -A POSTROUTING -o eth1 -j SNAT --to-source "public IP"
iptables -t nat -A PREROUTING -i eth1 -j DNAT --to-destination "private IP"
Restricted Cone NAT;
iptables -t nat POSTROUTING -o eth1 -p udp -j SNAT --to-source "public IP"
iptables -t nat PREROUTING -i eth1 -p udp -j DNAT --to-destination "private IP"
iptables -A INPUT -i eth1 -p udp -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -i eth1 -p udp -m state --state NEW -j DROP
Port Restricted Cone NAT;
iptables -t nat -A POSTROUTING -o eth0 -j SNAT --to-source "public IP"
Symmetric NAT;
echo "1" >/proc/sys/net/ipv4/ip_forward
iptables --flush
iptables -t nat -A POSTROUTING -o eth1 -j MASQUERADE --random
iptables -A FORWARD -i eth1 -o eth0 -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -A FORWARD -i eth0 -o eth1 -j ACCEPT