I built a root filesystem on arm. It should run dbus-daemon and avahi-daemon, but when I try to run avahi-daemon
$ dbus-daemon --system
$ avahi-daemon
I get this message:
Found user 'avahi' (UID 4) and group 'avahi' (GID 4).
Successfully dropped root privileges.
avahi-daemon 0.6.28 starting up.
WARNING: No NSS support for mDNS detected, consider installing nss-mdns!
dbus_bus_request_name(): Connection ":1.0" is not allowed to own the service "org.freedesktop.Avahi" due to security policies in the configuration file
WARNING: Failed to contact D-Bus daemon.
avahi-daemon 0.6.28 exiting.
What is wrong? Is it about dbus configuration ?
I had a similar problem, in my case the default avahi-dbus.conf that come with my system packet system just lack the last " </policy> " before " </busconfig> " which triggered this error.
I first thought the problem didn't come from this file since a rapid look at it is not enough to find this kind of syntax error.
In my case I simply had to restart the dbus service.
This probably was because avahi inserted a dbus config file (/etc/dbus-1/system.d/avahi-dbus.conf) which wasn't detected automatically.
There are restrictions on what client can register what name on the system bus. Otherwise a user process could receive request intended for some system service.
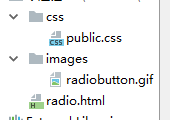
The restrictions are configured via the dbus-daemon configuration file, usually /etc/dbus-1/system.conf. In standard installations this file includes other config files, especially all in the /etc/dbus-1/system.d/ directory, where service specific configurations are stored. This way DBus is usually configured for Avahi:
Example from my workstation:
$ cat /etc/dbus-1/system.d/avahi-dbus.conf
<!DOCTYPE busconfig PUBLIC
"-//freedesktop//DTD D-BUS Bus Configuration 1.0//EN"
"http://www.freedesktop.org/standards/dbus/1.0/busconfig.dtd">
<busconfig>
<!-- Only root or user avahi can own the Avahi service -->
<policy user="avahi">
<allow own="org.freedesktop.Avahi"/>
</policy>
<policy user="root">
<allow own="org.freedesktop.Avahi"/>
</policy>
<!-- Allow anyone to invoke methods on Avahi server, except SetHostName -->
<policy context="default">
<allow send_destination="org.freedesktop.Avahi"/>
<allow receive_sender="org.freedesktop.Avahi"/>
<deny send_destination="org.freedesktop.Avahi"
send_interface="org.freedesktop.Avahi.Server" send_member="SetHostName"/>
</policy>
<!-- Allow everything, including access to SetHostName to users of the group "adm" -->
<policy group="adm">
<allow send_destination="org.freedesktop.Avahi"/>
<allow receive_sender="org.freedesktop.Avahi"/>
</policy>
<policy user="root">
<allow send_destination="org.freedesktop.Avahi"/>
<allow receive_sender="org.freedesktop.Avahi"/>
</policy>
</busconfig>
Make sure you have these standard configuration files or a proper custom configuration in place.