I want to de-activate TLSv1.0 with spring boot(release 1.3.3), but it doesn't work if application.yml as below:
ssl:
protocol: TLSv1.2
key-store: /E:/key/server.jks
key-store-password: serverpkcs12
I still can access web page if only choose "USE TLS 1.0" in IE.
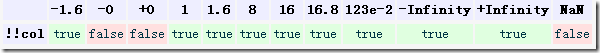
See this pic--not work.
However, if doesn't use embedded tomcat, and add these arguments for Connector located in server.xml, it works fine for me--web page blocked by IE. See this pic--worked for me
sslProtocols="TLSv1.2" sslEnabledProtocols="TLSv1.2"
And I also tried some VM arguments, for exmaple -Dhttps.protocols="TLSv1.2", all of them are useless.
So What can I do for this?
The most transparent and readable way is to explicitly configure the valid TLS protocols in your application configuration file by excluding - of course - the unwanted ones.
e.g. in YAML
server.ssl.enabled-protocols=TLSv1.1,TLSv1.2
You can then start your server and check whether TLSv1.0 is working by peforming the following
openssl s_client -connect localhost:443 -tls1
The above connections should be rejected whereas the following two will be accepted and print the certificate's details
openssl s_client -connect localhost:443 -tls1_1
openssl s_client -connect localhost:443 -tls1_2
A way that i found is to set ciphers that are supported only by TLSv1.2. Ex: If you will put in application.yml
server.ssl.ciphers:TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256,TLS_DHE_RSA_WITH_AES_256_GCM_SHA384,TLS_DHE_RSA_WITH_AES_128_GCM_SHA256,TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256,TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384,TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
And the using CURL
openssl s_client -connect example.com:443 -tls1
You will see that request will be ignored / rejected because that cipher that you set in application.yml will validate only TLSv1.2 requests.
My solution is
@Bean
public EmbeddedServletContainerFactory servletContainerFactory()
{
TomcatEmbeddedServletContainerFactory factory = new TomcatEmbeddedServletContainerFactory();
factory.addConnectorCustomizers(new TomcatConnectorCustomizer()
{
@Override
public void customize(Connector connector)
{
connector.setAttribute("sslProtocols", "TLSv1.1,TLSv1.2");
connector.setAttribute("sslEnabledProtocols", "TLSv1.1,TLSv1.2");
}
});
return factory;
}
And remove protocol: TLSv1.2 from application.yml
The answers so far only show how to lock-down TLS to a set of versions not yet considered broken. Since the question was how to de-activate a specific version, here's how using at least java 8:
String algs = Security.getProperty("jdk.tls.disabledAlgorithms");
// TODO: null/empty check on algs
Set<String> disabled =
Arrays.stream(algs.split(","))
.map(String::trim)
.collect(Collectors.toSet());
// TODO: inject these algs as properties for configurability
disabled.add("TLSv1");
algs = String.join(", ", disabled);
Security.setProperty("jdk.tls.disabledAlgorithms", algs);
Do this early on in your context initialisation before the Tomcat server is created and to be thorough you should catch SecurityException in case there's a policy in place that blocks the setProperty() call.
Using this method you benefit from new versions included in the JDK in the future.