I'm trying to allow legacy systems (CentOS 5.x) to continue making connections to services which will shortly allow only TLS v1.1 or TLS v1.2 connections (Salesforce, various payment gateways, etc.)
I have installed Squid 3.5 on a Centos 7 server in a docker container, and am trying to configure squid to bump the SSL connections. My thought was that since squid acts as a MITM and opens one connection to the client and one to the target server that it would negotiate a TLS 1.2 connection to the target, while the client was connecting with SSLv3 or TLS 1.0.
Am I totally off-base here, or is this something that should be possible? If Squid can't do this, are there other proxies which can?
My current squid configuration looks like this:
access_log /var/log/squid/access.log
cache_log /var/log/squid/cache.log
cache_store_log none
cache deny all
http_access allow all
http_port 3128 ssl-bump cert=/etc/squid/ssl_cert/myCA.pem generate-host-certificates=on version=1
ssl_bump stare all
ssl_bump bump all
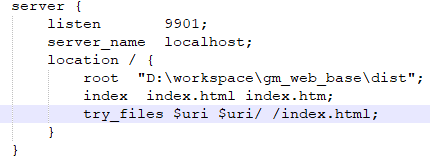
I was able to get this working by only bumping at step1, and not peeking or staring. The final configuration that I used (with comments) is below:
sslcrtd_program /usr/lib64/squid/ssl_crtd -s /var/lib/ssl_db -M 4MB
# Write access and cache logs to disk immediately using the stdio module.
access_log stdio:/var/log/squid/access.log
cache_log /var/log/squid/cache.log
# Define ACLs related to ssl-bump steps.
acl step1 at_step SslBump1
acl step2 at_step SslBump2
acl step3 at_step SslBump3
# The purpose of this instance is not to cache, so disable that.
cache_store_log none
cache deny all
# Set up http_port configuration. All clients will be explicitly specifying
# use of this proxy instance, so https_port interception is not needed.
http_access allow all
http_port 3128 ssl-bump cert=/etc/squid/certs/squid.pem \
generate-host-certificates=on version=1
# Bump immediately at step 1. Peeking or staring at steps one or two will cause
# part or all of the TLS HELLO message to be duplicated from the client to the
# server; this includes the TLS version in use, and the purpose of this proxy
# is to upgrade TLS connections.
ssl_bump bump step1 all