When trying to access the Graph Service Client using I am receiving the error :
Code: Authorization_RequestDenied
Message: Insufficient privileges to complete the operation.
After researching this error the most common solution was to set the permissions for the API. This had already been done and has permissions to read basic/full profiles.
I've delete and re-added the APIs.
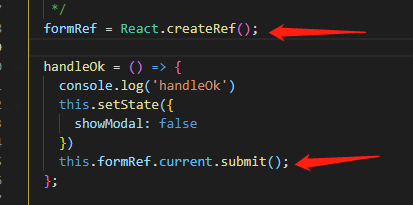
Below is the code in my AzureAuthenticationProvider class which inherits from IAuthenticationProvider:
public class AzureAuthenticationProvider : IAuthenticationProvider
{
private string _azureDomain = "myDevDom.onmicrosoft.com";
public async Task AuthenticateRequestAsync(HttpRequestMessage request)
{
try
{
string clientId = "2b823c67-1b0d-4a10-a9e1-737142516f5q";
string clientSecret = "xxxxxx";
AuthenticationContext authContext = new AuthenticationContext("https://login.windows.net/" + _azureDomain + "/oauth2/token");
ClientCredential credentials = new ClientCredential(clientId, clientSecret);
AuthenticationResult authResult = await authContext.AcquireTokenAsync("https://graph.microsoft.com/", credentials);
request.Headers.Add("Authorization", "Bearer " + authResult.AccessToken);
}
catch (Exception ex)
{
}
}
}
I've tried changing the client secret to an invalid Id and it threw an error, so the client key is correct. I've also tried to verify that the access token is valid by altering the access token, this also returns a error.
The above code seems to work fine.
Below is the code where I'm trying to access Azure AD:
public async Task<IGraphServiceUsersCollectionPage> GetUsersByLastName(string lastname)
{
GraphServiceClient graphClient = new GraphServiceClient(new AzureAuthenticationProvider());
string filter = String.Format("startswith(surname, '{0}')", lastname);
IGraphServiceUsersCollectionPage users = await graphClient.Users.Request().Filter(filter).GetAsync(); //Fails on this line
return users;
}
Any help is much appreciated, and thanks in advance for any help. 
Please refer to below steps :
From your screenshot , seems you grant Read and write directory data application permission for Windows Azure Active Directory(azure ad graph api) . Since you are using microsoft graph (https://graph.microsoft.com/) , you need to grant application permission for Microsoft Graph :

Since you are admin in your AAD, You could grant permission for users in organization by click Grant permission button shown in above screenshot .
Then you could use your code (client credential flow to get the token) and query users information . If you check the claims in access token issued by azure ad , you could find Directory.Read.All permission in roles claim .
 Make sure click "Grant Permissions" and than Yes for all users accounts.
Make sure click "Grant Permissions" and than Yes for all users accounts.
For me the key to solve this problem was hint:
To use the Graph API with your B2C tenant, you will need to register a dedicated application by using the generic App Registrations menu (All Services and there it is by default not Favourite starred) in the Azure Portal, NOT Azure AD B2C's Applications menu. You can't reuse the already-existing B2C applications that you registered in the Azure AD B2C's Applications menu.
Find more on page AD B2C API access demo
In some cases the actual issue happens because we use "Application permissions" instead of "Delegated permissions". In my application, I have tried to list all the users with application permissions and it wasn't working. When I switched to a delegated permissions, it worked.
So, some quick check would be like this:
- Check if you are using Microsoft Graph API or something else
- Use Delegated permissions
- Click Grant permissions button to propagate permissions :)
Hopefully, this would help someone.
It seems like your application is not having enough rights to access AD information. You can follow the steps mentioned in below link/article to login to Azure portal and see if your application has got enough privileges to access AD.
http://www.morgantechspace.com/2016/01/graph-api-insufficient-privileges-to-complete-the-operation.html
https://docs.microsoft.com/en-us/azure/active-directory-b2c/active-directory-b2c-devquickstarts-graph-dotnet
Also I hope, the "authResult.AccessToken" is not null in your case.
One thing, the second link above is having very detailed explanation on application access rights to AD. could be of help to you.
Suppose you want to create group in azure active directory
i have to performer the following steps to solve this problem
- AD > App Registered > your app
- Select Required Permission
- Click Add and select Microsoft Graph and add it
- select Microsoft Graph
- select Read and write all groups from delegated permission list
- And save it
- Select Windows Azure Active Directory and grant all application permission
- Save it
Grant permissions by ticking 'Directory.Read.All/ Write' is not enough.
I run into the same issue. and solved by adding service principle to administrator role.
If you application is created recently, this can be done Azure AD Powershell.
$pricinple = Get-AzureADServicePrincipal || Where-Object {$_.DisplayName -eq 'youappname'}
$role = Get-AzureADDirectoryRole | Where-Object {$_.displayName -eq 'Company Administrator'}
Add-AzureADDirectoryRoleMember -ObjectId $role.ObjectId -RefObjectId $pricinple.ObjectId
for detail, see https://docs.microsoft.com/en-us/powershell/module/Azuread/Add-AzureADDirectoryRoleMember?view=azureadps-2.0
If you application was created long time ago, you will need to use MSOnline.
see: https://docs.microsoft.com/en-us/powershell/module/msonline/Add-MsolRoleMember?view=azureadps-1.0
In my case, delete user was not working. I took below steps & it started working for me.
Go to Azure Active Directory > Roles and administrators > Click on 'User administrator' > click on '+ Add assignment' to add your app. (i.e. console app using AAD Graph REST API to interact with Azure Active Directory).
Hope it helps someone.