Are there any known ways for ast.literal_eval(node_or_string)'s evaluation to not actually be safe?
If yes, are patches available for them?
(I already know about PyPy[sandbox], which is presumably more secure, but unless the answers are yes then no, my needs are minor enough that I won't be going that far.)
The documentation states it is safe, and there is no bug relative to security of literal_eval in the bug tracker, so you can probably assume it is safe.
Also, according to the source, literal_eval parses the string to a python AST (source tree), and returns only if it is a literal. The code is never executed, only parsed, so there is no reason to be a security risk.
>>> code = '()' * 1000000
>>> ast.literal_eval(code)
[1] 3061 segmentation fault (core dumped) python2
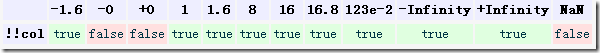
or possibly smaller will crash with SIGSEGV in Python 2. It might be exploitable under some conditions.