Someone (probably a bot) sent a request with the following URL to my ASP.NET 4.0 web forms application (running on IIS 7.0):
http://ipaddress-of-my-applications-domain/bla1.bla2.bla3.bla4.bla5:)
This caused an System.Web.HttpException. I received a logging email from ASP.NET HealthMonitoring I had configured, telling me:
A potentially dangerous Request.Path value was detected from the client (:).
Stack trace was:
System.Web.HttpRequest.ValidateInputIfRequiredByConfig()
System.Web.HttpApplication.PipelineStepManager.ValidateHelper(HttpContext context)
Why is a colon in the URL "potentially dangerous"? What dangerous things can be done with such a URL? Do I have any security hole here I am not aware of?
Thanks for explanation in advance!
Edit
I've tested that a colon in a query string (like http://mydomain.com?Test=9:)) does not cause this exception.
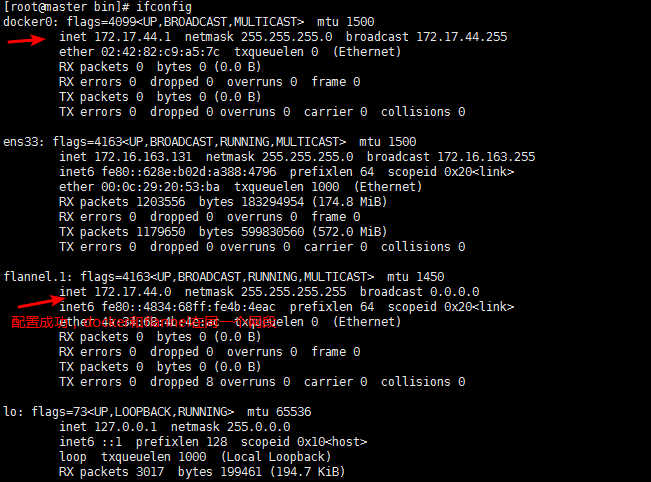
On NTFS, a given filepath can have multiple associated data streams. Apart from the main stream, also known as $DATA, there can be others, typically used to store metadata like the Internet Zone marker in downloaded files.
Alternate Data Streams are accessed using a colon separator, eg. file.dat:$DATA is an alternative way of saying file.dat. The presense of ADSs through the web has caused Microsoft some security issues in the past (eg. returning the source code of ASP pages instead of executing them), so as a precaution they're blocking the use of colon in the path part of the URL, as the path part often maps to the filesystem (though not in your case). This is less likely to occur from the query string so is not blocked there.
This is far from the worst false positive Request Validation will generate. Its anti-injection features are much worse. I personally would always disable it, as it's a stupid broken feature that can never actually make your webapp secure; only proper attention to string-escaping (and heavy sanitisation of anything you plan to use as a filename) can do that.
There are other characters that even if you turn Request Validation off you can't put in a path part for routing purposes. In particular, slashes (%2F, %5C, and byte sequences that would be invalid overlong UTF-8 sequences resolving to the same) and the zero byte. It's best to be conservative about what you put in paths in general.
I dont recollect exactly, but Internet Explorer is tied to operating system and it was able to perform some bad things like "con:sss" was able to open console and perform some batch commands etc, anything before colon is considered as protocol and windows allows you to override/create new protocols that can be opened and consumed by your dll. Anyone with greater experience of com and url monikers may give you very correct answer.
This is due to the request validation feature of ASP.NET, which prevents clients from attacking your website. The feature is enabled by default.
The following link explains better: http://www.asp.net/learn/whitepapers/request-validation