Regularly I need to investigate dumpfiles, always in the same way, and I'd like to automate this. I'm using Windbg as a tool, and I'm thinking of using Windbg scripting.
I have done some first attempts with PYKD, but I don't like the overhead that much, so I've opted for the standard Windbg scripting, but this is getting into a nightmare, let me show you what I want to do:
0:001> kb
# RetAddr : Args to Child : Call Site
00 00007ffc`26272685 : ffffffff`fffffffe 00007ff7`06e563f0 00007ff7`00000000 0000005a`1fb6fd70 : user32!NtUserGetMessage+0xa
01 00007ff7`06d87596 : 00000000`00000008 00007ff7`06e5d048 00000000`00007c1c 0000005a`00000004 : user32!GetMessageW+0x25
02 00007ff7`06d87673 : 0000005a`1f2b3710 00007ff7`06e5c7d0 0000005a`1f2ac270 00000000`00000002 : <Application>!CServiceModule::Run+0x8ee [sourcefile.cpp @ 1905]
03 00007ffc`26875ada : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : <Application>!CServiceModule::ServiceMain+0x63 [sourcefile.cpp @ 1379]
04 00007ffc`26ef13d2 : 00007ffc`26875aa0 0000005a`1f2ac270 00000000`00000000 00000000`00000000 : sechost!ScSvcctrlThreadA+0x3a
05 00007ffc`270454f4 : 00007ffc`26ef13b0 00000000`00000000 00000000`00000000 00000000`00000000 : kernel32!BaseThreadInitThunk+0x22
06 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : ntdll!RtlUserThreadStart+0x34
0:001> dx Debugger.Sessions[0].Processes[26520].Threads[14812].Stack.Frames[2].SwitchTo();dv /t /v
// The second command "dx ..." happens by clicking on the DML link of the line, corresponding with the line, containing "CServiceModule::Run".
Now, how to do this in a Windbg script?
- Launch the
kbcommand and put the result in a variable. (How to do that? I already tried usingasandaSbut neither seems to work) If I can't get the whole
kbresult in one variable, try to use a.foreach, as in following example:.foreach ( token { kb} ) { .printf "TEST\n" }=> even that is not working:
kbhas about 8 lines of results, while the wordTESTis printed 78 times.Instead of printing the word "TEST", print the variable
tokenand see what it looks like.
=> How to do that? I already tried.printf "%msu \n" , ${token}, or@$token, ... but nothing is working.Even if I get this working: how can I do string manipulation, decimal/hexadecimal number conversion, ...?
Not to forget: how do I compile such a script? I'm currently trying to run the script in Windbg, which sometimes gives compilation errors, but those are very unreadable (I add a new line, causing a problem, but the complication error (not a typo) does not even mention that newly added line).
You might say: just have a look at the examples, mentioned under this URL, but I can't find one example of a standard Windbg command, being run, and have its result stored in a variable (which is the first thing I need to do).
In case I get my script working, I might turn this post into a general "Windbg scripting FAQ" for the mentioned (and newly added) questions.
Edit after first answer
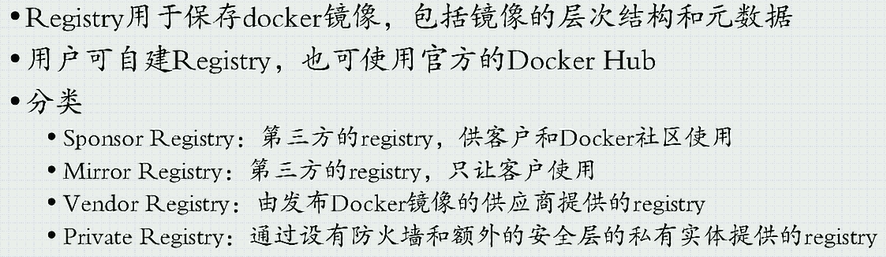
I realise that I've mistaken with the kb command: the actual command I need to use is ~* k, giving following result:

(Small remark: I've just a screenshot, instead of a text copy, in order to emphasize the DML hyperlinks)
As you can see, there are some DML results, and I would like to "click" on the line, containing CServiceModule::Run. When I do this by hand, there seems to be a translation towards the following command:
dx Debugger.Sessions[0].Processes[26520].Threads[14812].Stack.Frames[2].SwitchTo()
Here 26520 is the HexToDec conversion of 6798,
and 14812 is the HexToDec conversion of 39DC.
(Both to be retrieved from the screenshot's Id: 6798.39dc)
So I "need" the string manipulation and the HexToDec conversion in order to simulate DML clicking. If, however, you know an easier way to do put this "click" action into a script, I'd very very thankful!