WL.Client.InvokeProcedure is an internal API and used by Worklight Framework, however, you can call this API after connecting a device in Debug mode with Google Chrome. How can we restrict the access to WL.Client.invokeProcedure so that a user is not able to Exploit this call?
Steps to replicate (for Exploitation Only):
1. unpack an APK built by Worklight
2. Set the android:debuggable=true (also check how WL Adapters are being called in JS files)
3. Rebuild the APK
4. Install the APK in mobile
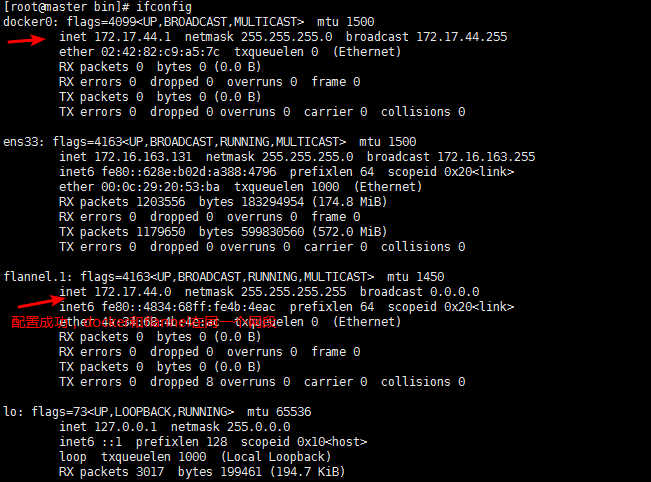
5. Start the Application and connect through Chrome://inspect
6. Authenticate as a "normal" user
7. Go to Developer Console
8. Invoke WL.Client.invokeProcedure for any adapter you are authenticated, but with unauthorized User Data
I think the test is a bit misleading since "you" as an attacker will have several prerequisites: have the technical skill of manipulate code, invoking code and know what is a "normal" user.
That said:
In the upcoming MobileFirst Platform v7.0 you will be able to obfuscate the code of a mobile app (iOS, Android and so on). You can also do this manually now.
Already now you can enable the Application Authenticity Protection feature as well as the webResourcesChecksumTest and webResourcesEncryption features. See the security element section in the Application Descriptor user documentation topic.
The above will add several layers of protection to your application, either preventing tampering with the application code, not allowing to use the app if its checksum has change and verify the application identity.